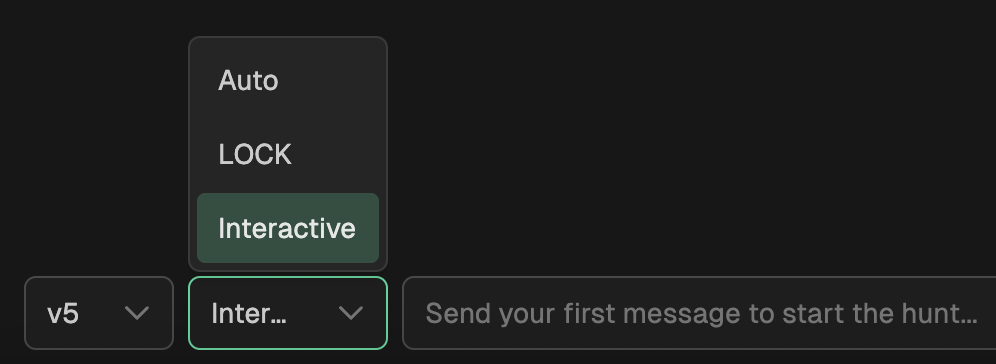
Hunt Modes
Customize how you engage with the vibe hunt agent to achieve hunt goals.
Available Modes
There are three hunt modes available to choose from in the platform. The first is Auto which is the default mode, the second is L.O.C.K. mode, and the third is Interactive mode.
Auto
Auto mode is a flexible, autonomous hunting workflow designed for efficiency and speed. When you provide a clear hunting objective, the assistant independently executes the necessary steps—researching context, running investigations, refining queries, and following evidence trails—without requiring approval at each checkpoint.
How it works:
- You provide a hunting goal with sufficient scope (threat, platform, timeframe, indicators).
- The agent chains investigations and research autonomously to test hypotheses.
- Checkpoints occur only when clarification is needed or when final results are ready.
- You maintain control over deliverables (rules, findings) and can redirect at any time.
Best suited for:
- Experienced threat hunters who prefer rapid results
- Well-defined hunt requests with clear indicators and scope
- Exploratory analysis where tactical decisions can be delegated
- Situations where speed is prioritized over step-by-step visibility
L.O.C.K.
L.O.C.K. Mode is a structured threat hunting methodology that guides you through a complete hunt lifecycle. Think of it as a checklist that ensures thorough, repeatable hunts.
How it works:
L — Learn
Gather threat intelligence and context before hunting.
- The agent researches the threat, technique, or behavior you want to hunt for.
- Review what data sources are available and what detection opportunities exist.
- Decide whether to proceed or adjust the research direction.
O — Observe
Form a clear hypothesis based on what we learned.
- The agent resends a hypothesis in the format: "Adversaries use [behavior] to [goal] on [target]".
- Identify expected indicators and why they're detectable.
- Decide whether to hunt with this hypothesis or refine it.
C — Check
Test the hypothesis through investigation and iterate.
- The agent runs investigations against your organization's security data.
- After each investigation, the agent presents findings and assesses progress.
- You decide whether to iterate with more angles, switch topics, or create a deliverable.
- Stop and review after every investigation without silent continuation.
K — Keep
Turn findings into actionable deliverables.
- Generate a detection rule (Sigma format).
- Update an existing rule.
- Document a security finding.
- After creating a deliverable, decide whether to create another, keep hunting, or start a new topic.
Key Principles
- Gated flow: Each phase requires your approval before moving forward.
- One step at a time: No skipping phases or merging steps.
- Always checkpoint: You stay in control at every decision point.
- Iterative: You can drill deeper, pivot, or restart at any time.
Interactive Mode
Like LOCK mode, Interactive mode will research and generate a hypothesis - but it will stop and look for more feedback from you throughout the hunt. For instance, before executing queries it will display the plan so you are able to make adjustments. This mode is geared towards someone more experienced or someone that wants to have more control over the hunt, and allows for better interaction with the agent for direction and flow of the hunt.
Updated about 2 months ago